Almost all the devices these days come with Bluetooth technology support. It is a highly beneficial way to connect devices and enjoy the source audio to another device. Using Bluetooth, you can even share files.
But there is a major limitation to the Bluetooth technology, which is that it is not fully secured. It is possible to access someone else’s Bluetooth device.
So, how a Bluetooth-enabled speaker, in particular, can be hacked? Let’s check it out!
Is it Possible to Hack My Bluetooth Speaker?
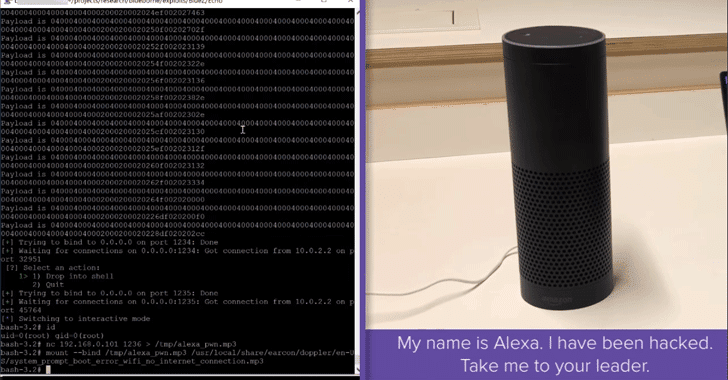
Before you move ahead you would be thinking that is it possible to hack a speaker with Bluetooth. The truth is yes!
You can not just hack the speaker but can get complete control over it. The procedure is quite complex and technical.
How to Hack a Speaker with Bluetooth?
You can follow one or more below-mentioned ways to hack a speaker.
Way 1 – Be the First One to Pair Up

The easiest way to connect to your speaker is by being the first one to pair up. This lets you have full control over the device.
Most of the speakers have a built-in default PIN. But if a speaker lacks this default PIN, it is easy to hijack it.
Way 2 – Use the Efficient KNOB Attack
Bluetooth is a standard technology that permits two devices to pair where one device is negotiated for the other.
The vulnerability is exploited by the Bluetooth KNOB or Key Negotiation of Bluetooth Attack to allow others for breaking the safety of Bluetooth. Distinct levels of safety are requested at varying levels for smooth communication. It enhances the compatibility of devices and makes the interaction between new and existing devices easier.
But this attack takes benefit of a drawback, which makes it simpler for a hacker to intervene between two devices. The KNOB method reduces the link’s entropy to a single byte. It is easy to hack a device when this encryption is weak.
For the KNOB process to function, the hijacker needs to be close to the Bluetooth devices, which are connected.
The steps you need to follow to perform are:
- Intensify the Attack
First, you need to escalate this attack. KNOB will open up the first door to intervene. But you need to escalate it more by leveraging access to a decrypted link and hacking the Bluetooth.
- Establish a Middle-Man Attack
Once it is escalated, you need to set up a relay for the MITM or Man in the Middle.
This will complete your attack. You have to write the Python script for changing the running session using MITM before transferring the reformed packets. It can be done by changing the audio in the playlist being played on the speaker.
With the help of this attack, you can hack the speaker without letting the user know about it.
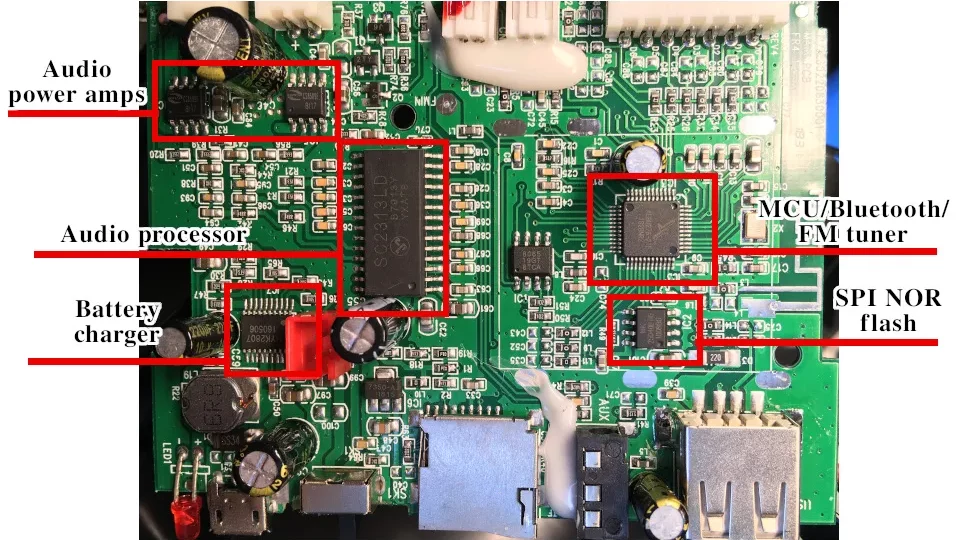
Way 3 – Identify Weaknesses in A Speaker

Most Bluetooth speakers possess firmware vulnerabilities. If such vulnerabilities are reachable by the attacker, it can exploit them and get full control over your speaker.
You can identify the vulnerability in your speaker by scanning it using software, such as Shodan. This software searches online for all devices connected to your speaker. It also helps you find devices with vulnerabilities.
You can also conduct a Google search using a vulnerability scanner tool to determine security issues or weaknesses in your speaker. By performing the search, you can find distinct websites, which let you scan for issues in the Bluetooth devices.
Way 4 – Use Metasploit for Hacking
Metasploit is a great way to hack any speaker. It is a testing framework, which lets you exploit the vulnerabilities. It incorporates a ‘bluetooth_hcidump’ module, which is useful for hijacking Bluetooth.
To use this framework, you have to follow these steps:
- Look for a susceptible Bluetooth device, which is linked to another device online.
- Take control over the device utilizing ‘bluetooth_hcidump.’ It is useful for capturing and analyzing the Bluetooth packets.
- Next use a ‘btscanner; tool for finding Bluetooth devices, which are open to attacks.
Way 5 – Hack Bluetooth Speaker Using Kali Linux
There is another proven way to hack a Bluetooth-enabled speaker, which is Kali Linux. This tool helps to identify issues in Bluetooth speakers. It is a testing platform to check the penetration of an operating system and comes with multiple tools. All these tools are useful to attack and hack Bluetooth devices.
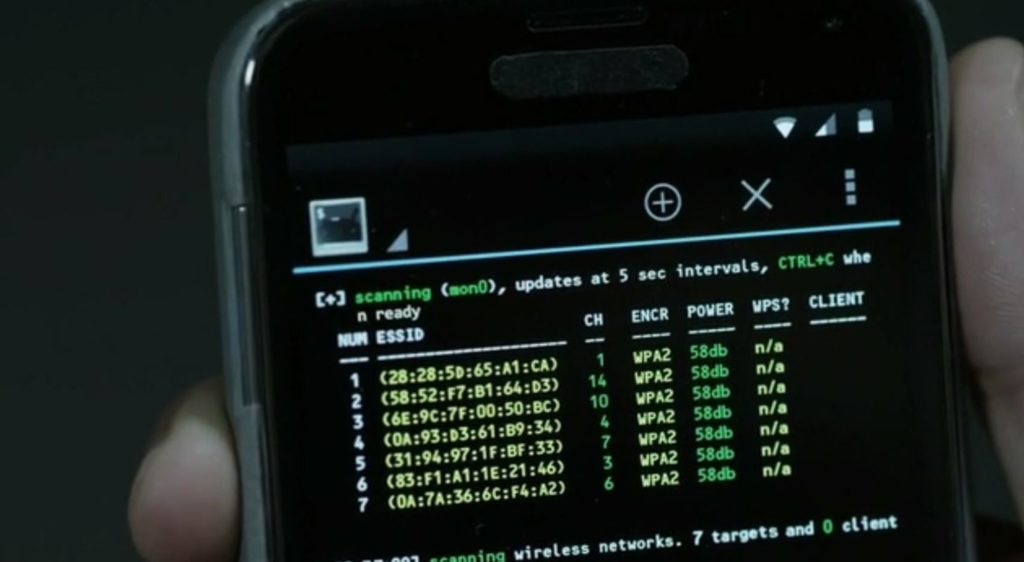
By using the Bluetooth-hcidump tool in Kali Linux, you can identify issues in any Bluetooth speaker. It lets you capture and assess the various elements of the Bluetooth packet.
You may use its ‘Btscanner’ feature in this tool, using which you can identify Bluetooth devices, which are open to attacks.
This software is available for free from Kali.com. You need to download and install it.
How Can You Prevent Bluetooth Speaker from Being Hacked?

You see, there are numerous ways following which you can hack a speaker. However, you can safeguard your speaker from getting hacked by following some preventive measures.
- Update the Firmware
Regularly update your speaker’s firmware. This fixes all vulnerabilities from your existing device’s firmware and makes sure the network is protected from the latest hacks and safety issues.
- Create a Strong Password for Security
Establish a strong password to keep the security strong. Let it be difficult for the hackers to guess the password.
- Turn Off Your Bluetooth When You are Not Using It
Make sure that you always keep the Bluetooth of your device off if it is not used. The hackers or hijackers cannot conquer it if it is switched off.
- Utilize a Robust Encryption Protocol
When you have a strong encryption protocol, it is difficult for someone to hack the Bluetooth speaker.
- Make Your Bluetooth Undiscoverable
You can protect Bluetooth speakers from being hacked by making them undiscoverable. This will make it difficult for others to find it.
- Use a Security Firewall
You can protect Bluetooth speakers with an Android or iPhone device using a firewall. It prevents others from identifying vulnerabilities in your Bluetooth network and entering into it.
- Avoid Pairing Your Device in Public
Try to not pair up your device with a common device in public as it is more prone to attacks or vulnerabilities. Make sure you pair only with your private Bluetooth speaker.
- Using Wired Connections in Public Areas
You might want to connect your speaker to your laptop or computer in a public area. Don’t use Bluetooth for the same, instead use an audio jack or an AUX cable.
- Use an App to Maintain Bluetooth Security
The Internet offers you a host of Bluetooth security apps, which are useful in protecting the device. Such apps let you establish a strong security code, keep your device undiscoverable, and update the firmware.
Important Things You Must Know

Can I notice whether my speaker is hacked or not?
Most of the time, it is not possible to know whether your speaker is hacked or not. But you can look for some malicious signs such as slowdown of the sound quality, sudden noise coming from your device, and frequent breaking of the connection.
What can I do for my hacked speaker?
You must turn off the Bluetooth speaker immediately if you feel it is hacked. Call the device’s manufacturer and ask for necessary support.
Can I remove the hacker from my Bluetooth speaker?
Yes, you can! You will require technical assistance in this context.
Conclusion
Hacking Bluetooth speakers is not an easy task. You need to be an expert to hack such devices. And if you want to keep Bluetooth speakers from being hijacked the best way out is to use a strong password and keep changing it regularly.
- 10 Home Recording Studio Equipment [Updated List] 2026

- Why Do My AirPods Sound Muffled After Update? 5 Working Solution

- What Is cVc Noise Cancellation? Guide to Crystal Clear Calls [2026]
- How to Stop Bluetooth Interference From WiFi Routers | Most Common Issue
- How to Use Bluetooth to Connect Your Phone to Your Car | 3 Step Process

- How Does Apple’s H1 and H2 chips Works? what are the Benefits [2026]